Mac Gatekeeper vulnerability allows installation of malware
A flaw with the Gatekeeper authentication feature in macOS, a tool designed to keep malware off Mac, is reportedly being exploited to deliver a malicious software package nicknamed "OSX/Linker."
The exploit, discovered by security researcher Filippo Cavallarin, relies on two basic Mac features to function: automount and Gatekeeper.
As detailed by Tom's Guide, Gatekeeper funnels files downloaded from the internet to Apple's XProtect antivirus screener, but grants files from a local storage device -- mounted via automount -- safe passage without scrutiny. Cavallarin was able to trick Gatekeeper into thinking a downloaded file originated from a local drive, bypassing the normal screening protocols.
Cavallarin reportedly contacted Apple about the issue in February, but published details on May 24 since the problem was left unfixed.
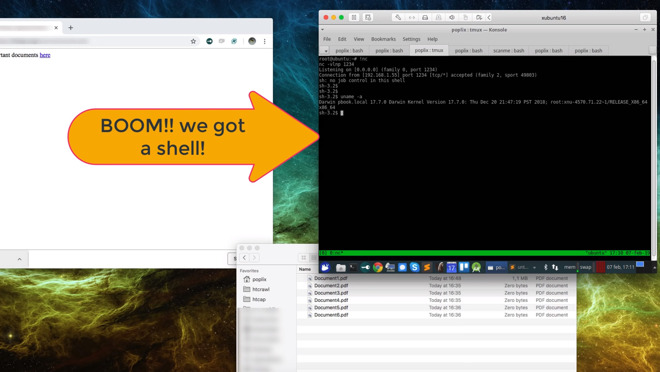
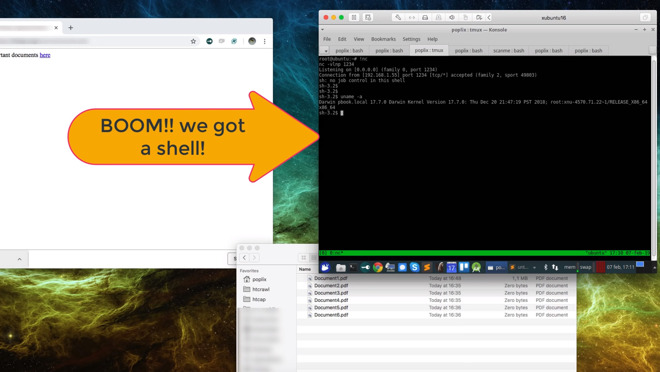
The accompanying OSX/Linker malware attempts to hijack a Mac, at which point the computer can be used for any malicious activity attackers want, from crytpo mining to data theft.
The code has been uploaded four times to VirusTotal, a repository researchers use to detect and share malware samples. That's a relatively small amount, and the malware is already being screened by Intego software and likely other antivirus tools as well.
It should therefore be relatively easy to avoid OSX/Linker, especially by following standard protocols like refusing downloads from unknown sources. It's also possible to disable automounting, though that would require users to manually connect and disconnect external drives each time they're used.
The exploit, discovered by security researcher Filippo Cavallarin, relies on two basic Mac features to function: automount and Gatekeeper.
As detailed by Tom's Guide, Gatekeeper funnels files downloaded from the internet to Apple's XProtect antivirus screener, but grants files from a local storage device -- mounted via automount -- safe passage without scrutiny. Cavallarin was able to trick Gatekeeper into thinking a downloaded file originated from a local drive, bypassing the normal screening protocols.
Cavallarin reportedly contacted Apple about the issue in February, but published details on May 24 since the problem was left unfixed.
The accompanying OSX/Linker malware attempts to hijack a Mac, at which point the computer can be used for any malicious activity attackers want, from crytpo mining to data theft.
The code has been uploaded four times to VirusTotal, a repository researchers use to detect and share malware samples. That's a relatively small amount, and the malware is already being screened by Intego software and likely other antivirus tools as well.
It should therefore be relatively easy to avoid OSX/Linker, especially by following standard protocols like refusing downloads from unknown sources. It's also possible to disable automounting, though that would require users to manually connect and disconnect external drives each time they're used.

Comments
1. Don’t EVER accept a Flash update from anywhere other than Adobe. In fact don’t use Flash unless you absolutely have to.
2. Make sure your browser settings prohibit launching any download automatically.
3. If it smells fishy it probably is. Don’t open it.
But people being people... well you know.
#2 MacOS needs a good antivirus program
Apple’s lack of transparency, lack of a bug bounty program, and (in this case) lack of bugs getting fixed in a timely manner, means additional steps are needed to protect yourself.
MacOS provides a better user experience than Windows, but in some ways it’s inferior. I suspect MacOS are just a lower priority vs iOS, and doesn’t get Apple’s full attention.
I agree, common sense is a good start to security, but who isn’t void of common sense occasionally...?
Ad networks distribute malware by means of several obscure redirections. Even if you don't click anything on the infected page, anything as in not only the ad but nothing on that page, the payload is sent to your computer. The display of the wrapper ad is enough to infect your computer. The payload mostly comes in one of the archive formats such as .zip, .dmg, .pkg, that list being not exhaustive. You may want to check your Downloads folder right now and move all of the said archive files to the Trash, don't even try to open any of them, you can download legitimate installers anytime from the legitimate sources.
Download by redirection may occur on any web page, not only ads. Be careful when binge browsing expecially on questionable sites, watch what your browser does after clicking a link, does the link open a pop-up window or does it redirect to a download before opening the target page? And check your Downloads folder frequently to spot any suspicious download.
As in easy to have secured them
begs the the question about backdoors. Rather than build one outright, just leave a quiet vulnerability.
This is one in particular is ridiculous.
This is just clickbait and everybody and their dog jumps on it because it has "Apple" and "vulnerabilty" in the headline.
I had expected a bit more research from AI before publishing on such a delicate topic.
In the very few cases of people genuinely needing to use the Flash flash player (legacy web sites, etc.), people should use Chrome. It has Flash baked in and uses its own update mechanism, avoiding the whole fake Flash installer issue.
But yeah, people being people...
I guess they were too busy updating the Animoji to be bothered with something minor like online security of the OS.
True.
But in 2019, I cannot imagine who needs Flash. I do not have it installed and have not seen media requiring Flash anywhere for a very long time.
Malware is a general term for all types of harmful or deceptive and unruly software.
Malign
Malignent
2) enable "show all file extensions" for finder
3) notice his PDF.app file doesn't have the folder twister like the parent folder he just opened (granted this is subtle)
Can someone explain:
He says PDF is an app with a folder icon, why when he opens it does it update finder view to a list of Document.pdf files?
Why does opening document.pdf open a terminal inside what appears to be a xubuntu VM? That seems needlessly indirect vs just having it pop open textedit or something... on the mac itself.
1) most of the paranoids here don't read what other people write
2) you all use untrusted NFS mounts
This is the only explanation why people are still posting tips about dealing with this overblown non-existant "exploit".
99.99% of all Mac users don't use an NFS share and if they do, they trust them in 99.99% of all cases. So why are you guys still discussing this click bait crap???
I'm pretty sure NFS has been routable since forever? It certainly was back in the mid 90s.