iOS bug prevents VPN apps from encrypting all traffic
An unpatched bug present in iOS 13.3.1 and later could keep a virtual private network (VPN) from fully encrypting all traffic, leaving data and IP addresses exposed.
The vulnerability, disclosed by a ProtonVPN user, impacts all VPN services on recent versions of iOS
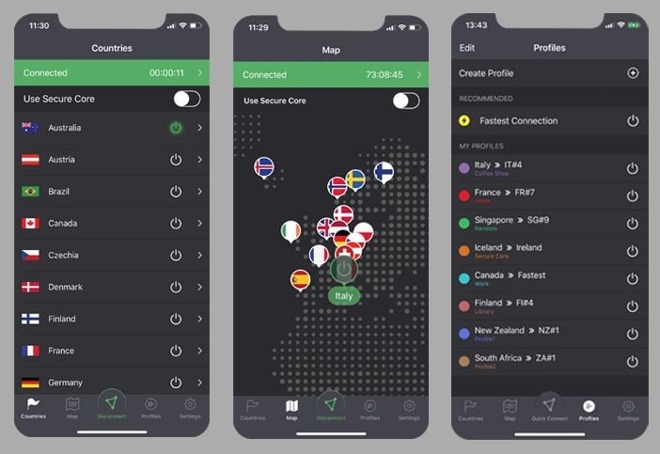
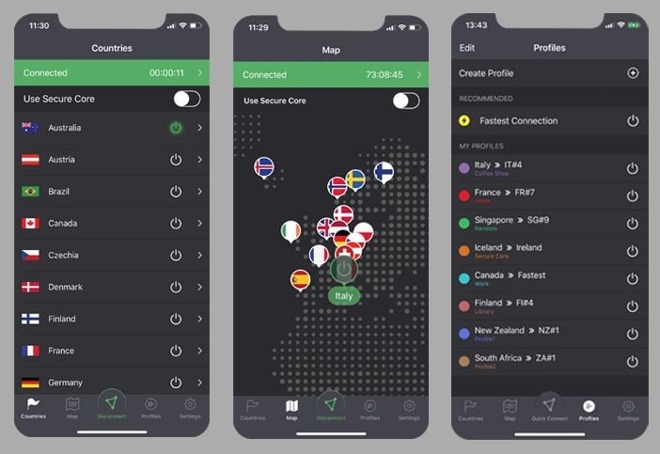
VPNs work by routing your internet traffic through a secure tunnel, keeping your browsing activity both private and encrypted. Apple's mobile devices, like iPhone and iPad, have long supported both employer-issued VPNs and third-party options available on the App Store.
But a security vulnerability disclosed by ProtonVPN and shared with Bleeping Computer could keep VPNs on iOS and iPadOS from working properly, potentially leading to data leaks.
Impacted versions of iOS, including the latest iOS 13.4, fail to close existing internet connections when a user connects to a VPN. Typically, when opening a VPN, the OS terminates all previous connections and automatically reestablishes links to original destination servers through the VPN tunnel. That process is not occurring in recent versions of iOS.
Instead, iOS keeps some existing connections alive outside of the VPN tunnel, where data isn't encrypted. These connections, which can remain open for minutes or hours, could potentially reveal a user's location, leak their IP address, or expose them and the servers they're communicating with to attack.
Normally, those risks are fairly benign for the average user, but ProtonVPN explains that the people who rely on VPNs the most may be vulnerable to the direst consequences.
"Those at highest risk because of this security flaw are people in countries where surveillance and civil rights abuses are common," the company writes.
ProtonVPN offers Apple's push notifications, whose connections to Apple's servers aren't terminated when connecting to a VPN, as an example. But the VPN maker notes that the bug can affect any app running on a user's device.
The bug cannot be fixed by a third-party VPN app, since Apple's tight sandboxing restrictions on iOS prevent them from terminating existing connections.
According to Bleeping Computer, Apple is aware of the issue and is currently working on mitigating it. While Apple recommends users enable Always-on VPN, that feature won't work for those who use third-party VPN apps.
Until Apple issues a fix, ProtonVPN recommends enabling and disabling Airplane Mode to manually kill connections after connecting to a VPN. The VPN maker warns that the workaround isn't 100% effective, however.
The VPN bypass vulnerability was first discovered in 2019 by a security researcher who is part of the Proton community. Along with ProtonVPN, Swiss-based security company Proton is well-known for their privacy-focused email client, ProtonMail.
The vulnerability, disclosed by a ProtonVPN user, impacts all VPN services on recent versions of iOS
VPNs work by routing your internet traffic through a secure tunnel, keeping your browsing activity both private and encrypted. Apple's mobile devices, like iPhone and iPad, have long supported both employer-issued VPNs and third-party options available on the App Store.
But a security vulnerability disclosed by ProtonVPN and shared with Bleeping Computer could keep VPNs on iOS and iPadOS from working properly, potentially leading to data leaks.
Impacted versions of iOS, including the latest iOS 13.4, fail to close existing internet connections when a user connects to a VPN. Typically, when opening a VPN, the OS terminates all previous connections and automatically reestablishes links to original destination servers through the VPN tunnel. That process is not occurring in recent versions of iOS.
Instead, iOS keeps some existing connections alive outside of the VPN tunnel, where data isn't encrypted. These connections, which can remain open for minutes or hours, could potentially reveal a user's location, leak their IP address, or expose them and the servers they're communicating with to attack.
Normally, those risks are fairly benign for the average user, but ProtonVPN explains that the people who rely on VPNs the most may be vulnerable to the direst consequences.
"Those at highest risk because of this security flaw are people in countries where surveillance and civil rights abuses are common," the company writes.
ProtonVPN offers Apple's push notifications, whose connections to Apple's servers aren't terminated when connecting to a VPN, as an example. But the VPN maker notes that the bug can affect any app running on a user's device.
The bug cannot be fixed by a third-party VPN app, since Apple's tight sandboxing restrictions on iOS prevent them from terminating existing connections.
According to Bleeping Computer, Apple is aware of the issue and is currently working on mitigating it. While Apple recommends users enable Always-on VPN, that feature won't work for those who use third-party VPN apps.
Until Apple issues a fix, ProtonVPN recommends enabling and disabling Airplane Mode to manually kill connections after connecting to a VPN. The VPN maker warns that the workaround isn't 100% effective, however.
The VPN bypass vulnerability was first discovered in 2019 by a security researcher who is part of the Proton community. Along with ProtonVPN, Swiss-based security company Proton is well-known for their privacy-focused email client, ProtonMail.

Comments
The other thing I don't like is that while you're trying to establish a VPN connection, your device has already probably communicated with all your major accounts over the unsecured network (ie. coffee shop, airport, etc.).
You’re so embarrassingly incompetent sometimes...
I agree that it's not actually a bug, just a minor inconvenience for the few users that alternate between non-VPN and VPN connections.
Also - maybe I'm misunderstanding Airplane Mode - but would the VPN connect with Airplane Mode on?
Minor inconvenience for the few users? Don't most people use VPNs like that?
There’s actually two types on iOS. Split vpn and full tunnel. Split allows some stuff to be routed elsewhere. Full tunnel tunnels everything.“
Finally some one that understands that this is not a vulnerability but expected behavior. Split tunnel is the most compatible with most apps and full tunnel will causes issues with some applications due to latency Siri will time out or notifications will come through few seconds later. Encrypted DNS servers also work through split and full tunnel. It’s up to user to decide if given the option. But some experts believe that split tunnel is less secure. The point is it’s not a vulnerability and no fix is coming.