After China malware infiltration, Apple helps developers ensure their Xcode install is leg...
Apple on Tuesday issued a notice to developers, informing them how they can make sure their copy of Xcode is legitimate -- a precaution necessitated by the appearance of malware on the iOS App Store in China.
Those malicious apps were built with a counterfeit version of Xcode, which developers may have been prompted to download from outside sources because of Internet speed and connectivity issues in China. As a result, Apple instructed developers to download Xcode directly from the Mac App Store or from its developer website, and to leave Gatekeeper enabled on all of their systems to protect against tampered software.
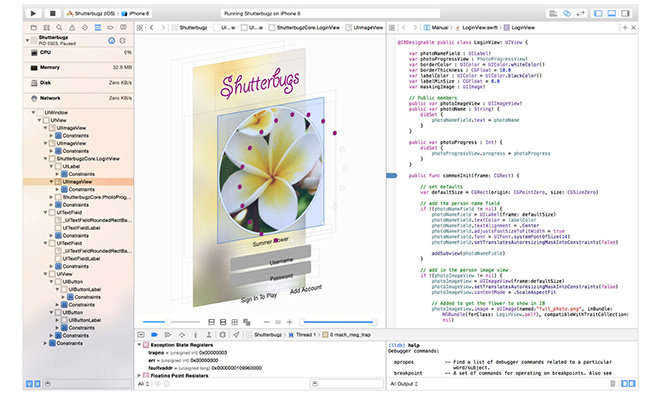
Developers can verify their copy of Xcode is legitimate by opening terminal on a Gatekeeper-enabled system and typing the following:
Developers who are not running a legitimate copy of Xcode are advised to download a clean copy from the Mac App Store or Apple's developer site, and to recompile their applications before submitting them for review.
Apple confirmed on Sunday that modified versions of Xcode were used to successfully infiltrate malware into the iOS App Store. In all, about 40 infected apps made it through, including WeChat and ridesharing service Didi Kuaidi.
The malicious copies of Xcode were hosted on cloud storage run by China's Baidu, and those copies have since been removed. Developers running a modified version of Xcode would have needed to disable Apple's Gatekeeper security feature in order to run the software.
Chinese developers turn to alternative download sources hosted on local servers, because downloads from Apple's own servers can be very slow within the country.
Those malicious apps were built with a counterfeit version of Xcode, which developers may have been prompted to download from outside sources because of Internet speed and connectivity issues in China. As a result, Apple instructed developers to download Xcode directly from the Mac App Store or from its developer website, and to leave Gatekeeper enabled on all of their systems to protect against tampered software.
Developers can verify their copy of Xcode is legitimate by opening terminal on a Gatekeeper-enabled system and typing the following:
In the example above, /Applications/ should be the directory where Xcode is installed. The tool can take a few minutes to complete, but if a user has a legitimate copy of Xcode installed from the Mac App Store, it will return the following:spctl --assess --verbose /Applications/Xcode.app
And for legitimate copies of Xcode downloaded from Apple's developer website, the tool will return either of the following responses:/Applications/Xcode.app: accepted
source=Mac App Store
If the returned result says anything other than "accepted," or the source reads anything other than "Mac App Store," "Apple System" or "Apple," then the application signature is not valid for that copy of Xcode./Applications/Xcode.app: accepted
source=Apple
/Applications/Xcode.app: accepted
source=Apple System
Developers who are not running a legitimate copy of Xcode are advised to download a clean copy from the Mac App Store or Apple's developer site, and to recompile their applications before submitting them for review.
Apple confirmed on Sunday that modified versions of Xcode were used to successfully infiltrate malware into the iOS App Store. In all, about 40 infected apps made it through, including WeChat and ridesharing service Didi Kuaidi.
The malicious copies of Xcode were hosted on cloud storage run by China's Baidu, and those copies have since been removed. Developers running a modified version of Xcode would have needed to disable Apple's Gatekeeper security feature in order to run the software.
Chinese developers turn to alternative download sources hosted on local servers, because downloads from Apple's own servers can be very slow within the country.

Comments
I was hoping they'd find a way of detecting applications that weren't built with a legit copy of Xcode.
The best way to detect that is to scan the binary for malware, effectively Apple has to use a 'virus' scanner when accepting an app.
We all know that that's as effective as taking a flu shot (although it is effective as a base income for the pharmaceutical industry) and makes all new cases undetectable.
$ spctl --assess --verbose /Applications/Xcode.app
See https://developer.apple.com/news/?id=09222015a
https://support.apple.com/en-us/HT202491
Maybe Apple will release a version of Xcode for iOS now?
The only pitfall at this moment is the yailbreak community; maybe declare that illegal?
Come to think of it, Apple could start another huge cloud service and offer an online build system, you only have to submit your sources - encrypted of course, Apple cannot touch them - and render most CPU power useless like most other cloud services.
As intrusive as the Chinese government is with their citizens, I don't believe for a second that they had no knowledge of this beforehand.
Apple confirmed on Sunday that modified versions of Xcode were used to successfully infiltrate malware into the iOS App Store. In all, about 40 infected apps made it through, including WeChat and ridesharing service Didi Kuaidi.
According to some estimates the number of infected apps is 3,418.
Not sure how valid that number is but it's at least worth considering more than 40 have been infected.
http://researchcenter.paloaltonetworks.com/2015/09/more-details-on-the-xcodeghost-malware-and-affected-ios-apps/
Another way to do this is to disable sideloading for OS X, effectively make it iOS.
Maybe Apple will release a version of Xcode for iOS now?
The only pitfall at this moment is the yailbreak community; maybe declare that illegal?
Come to think of it, Apple could start another huge cloud service and offer an online build system, you only have to submit your sources - encrypted of course, Apple cannot touch them - and render most CPU power useless like most other cloud services.
Words fail me.
Maybe Apple should just pull out of China in every sense. Looks like Google's approach was far sighted and was the right course to take.
The correct Terminal command should be (notice the double minus signs):
spctl --assess --verbose /Applications/Xcode.app
I still have no idea how they were able to decompile or reverse engineer such a huge application. Perhaps they were able to find some resource folder that they could swap out some identically named files with added functionality. Anybody heard how the hack was done?
I still have no idea how they were able to decompile or reverse engineer such a huge application. Perhaps they were able to find some resource folder that they could swap out some identically named files with added functionality. Anybody heard how the hack was done?
Ask the hacking unit for the Chinese military.
Why would any honest developper get Xcode anywhere else but from the Mac App Store or Apple.com ?
I think every hacked copy of Xcode was downloaded knowingly and with ill intent and that this was Apple's politically correct way of warning those so-called 'developers' using such a copy that Apple are looking at them. Perhaps next time Apple will simply and rightfully revoke their license and keep those credentials close at hand.
Because China's internet access is incredibly slow (3.7 Mbit average) and then crippled by the Great Firewall, which pipes ALL international traffic through only THREE portals, where it is analyzed and filtered, further slowing it down.
If you're a huge developer, with hundreds of apps in the store, waiting for a multi-gigabyte download from overseas will completely halt your entire workforce for DAYS.
So you download off a local server, instead.
Or at least, you used to, until this happened.
Source: http://qz.com/506582/chinas-awful-internet-speed-has-spread-malware-to-millions-of-smartphones/
We've known since Snowden that the United States are all about stealing trade and other secrets from their supposed allies, too.
It's all par for the course in international politics. You're not exceptional, and neither is China, except that China is actually more or less successfully isolating itself from outside influences.
In other words, what's getting Americans' gall is that China isn't as open to the same kind of attacks that the U.S. would like to perpetrate, and in fact, are perpetrating on most other industrial nations, including all the ones they're "friends" with.
We've known since Snowden that the United States are all about stealing trade and other secrets from their supposed allies, too.
It's all par for the course in international politics. You're not exceptional, and neither is China, except that China is actually more or less successfully isolating itself from outside influences.
In other words, what's getting Americans' gall is that China isn't as open to the same kind of attacks that the U.S. would like to perpetrate, and in fact, are perpetrating on most other industrial nations, including all the ones they're "friends" with.
China industry has shit to steal, so off course they're not a target...
The west would hit mostly millitary and governmental installations rather than industry one; and If you think that Chinese hacker are better than the west, you are kidding yourself. China would simply not admit to any hacking unless it has too; it would be losing face to do so.
The Us probably spends 10 times more on cyber warfare than any one else in the world, including China.
In this case, this was aimed more at Chinese people than people outside; so do you respect the fact China likes to f*up their own people? YEah.. So, much greatness there.
Because China's internet access is incredibly slow (3.7 Mbit average) and then crippled by the Great Firewall, which pipes ALL international traffic through only THREE portals, where it is analyzed and filtered, further slowing it down.
If you're a huge developer, with hundreds of apps in the store, waiting for a multi-gigabyte download from overseas will completely halt your entire workforce for DAYS.
So you download off a local server, instead.
Or at least, you used to, until this happened.
Source: http://qz.com/506582/chinas-awful-internet-speed-has-spread-malware-to-millions-of-smartphones/
Really, this huge Chinese devellopper has no speedy Internal network, something US companies had 35 years ago... And every single node of this internal network is connected at the same speed to the outside world, even the ones in Hong Kong... Seems not likely at all for a big devellopper. If that's the case they should whoever's the CIO or CTO of this crap house should retire right now because they're not worthy of the title.