GrayShift's GrayKey iPhone forensics tool disassembled in FCC photos
New images of GrayShift's GrayKey have surfaced via an FCC filing, giving a close look at the iPhone unlocking device in use by law enforcement officials to gain access to secured iPhones.

A side view of the GrayKey tool
The GrayKey device first gained notoriety in 2018, as a relatively inexpensive encryption bypass tool primarily intended for use by the police and law enforcement organizations. It is meant to allow investigators entry to a locked iPhone, without requiring the user's permission.
Relatively few photographs of the device have been distributed, with the company and its clients attempting to maintain secrecy about it. Earlier releases revealed it to consist of a small gray square box with two cables sticking out, intended for connection to mobile devices, but not much further information stemmed forth about its design.

The LEDs and Lightning cables at the front of the GrayKey unit
In FCC filings first reported by Motherboard, the GrayKey is shown to have remarkably few external details. On one side, there are three LEDs, with two above each of the short Lightning cables and one in the middle above the label "Status," while on the back are ethernet and USB ports used to connect it to a computer for reading the data, and a power socket.
On the base is a sticker advising of support and sales website and email addresses, and a phone number.
Opening up the GrayKey, the device is found to be made using an ARM processor from Compulab. A mainboard at the base is protected by a metal plate, which has a further loosely-fitted slim board attached on top to connect the Lightning cables to the rest of the circuitry.
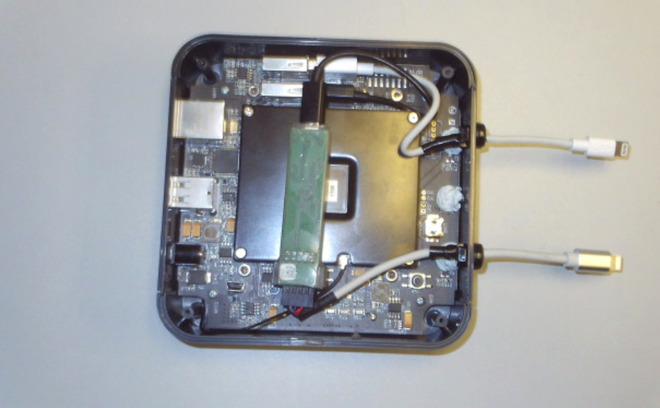
An FCC teardown of the GrayKey
Some of the images for the internals has an SSD on top of the mainboard, though the design of the device suggests the drive isn't actually part of the assembly. It seems likely that the SSD is put in place to hide the underside of the circuit board.
Devices sold in the United States typically have to be submitted to the FCC to acquire an FCC ID, meaning it will comply with FCC standards and is safe for sale. Given the nature of GrayKey, it seems unusual that a security device used by law enforcement would be subjected to less than secretive treatment such as an FCC filing.
GrayShift has found many clients for the GrayKey, as law enforcement grapples with the issue of wanting to gain access to devices owned by suspects, but are unable to secure a passcode or to pass biometrics to do so without the suspect's cooperation. The device has reportedly been used in some high-profile investigations, including one by the FBI in late 2019 where it was allegedly used to gain access to a locked iPhone 11 Pro Max.
In March, GrayShift started to market a software tool that could be used to reveal an iPhone's passcode without cracking the device. The digital forensics tool named "Hide UI" reportedly consists of spyware that can be installed via GrayKey and acts as a keylogger, one that monitors for when the user enters their passcode.

A side view of the GrayKey tool
The GrayKey device first gained notoriety in 2018, as a relatively inexpensive encryption bypass tool primarily intended for use by the police and law enforcement organizations. It is meant to allow investigators entry to a locked iPhone, without requiring the user's permission.
Relatively few photographs of the device have been distributed, with the company and its clients attempting to maintain secrecy about it. Earlier releases revealed it to consist of a small gray square box with two cables sticking out, intended for connection to mobile devices, but not much further information stemmed forth about its design.

The LEDs and Lightning cables at the front of the GrayKey unit
In FCC filings first reported by Motherboard, the GrayKey is shown to have remarkably few external details. On one side, there are three LEDs, with two above each of the short Lightning cables and one in the middle above the label "Status," while on the back are ethernet and USB ports used to connect it to a computer for reading the data, and a power socket.
On the base is a sticker advising of support and sales website and email addresses, and a phone number.
Opening up the GrayKey, the device is found to be made using an ARM processor from Compulab. A mainboard at the base is protected by a metal plate, which has a further loosely-fitted slim board attached on top to connect the Lightning cables to the rest of the circuitry.
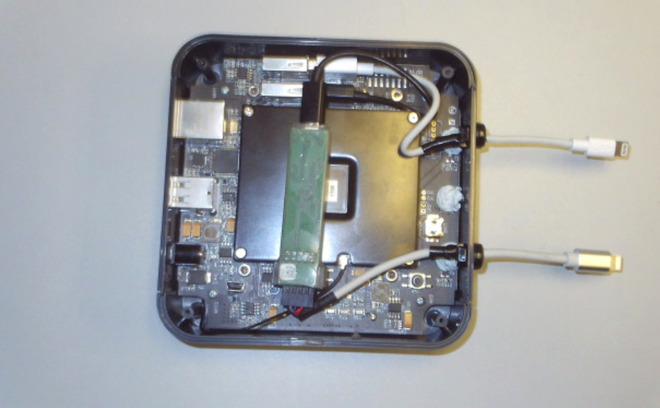
An FCC teardown of the GrayKey
Some of the images for the internals has an SSD on top of the mainboard, though the design of the device suggests the drive isn't actually part of the assembly. It seems likely that the SSD is put in place to hide the underside of the circuit board.
Devices sold in the United States typically have to be submitted to the FCC to acquire an FCC ID, meaning it will comply with FCC standards and is safe for sale. Given the nature of GrayKey, it seems unusual that a security device used by law enforcement would be subjected to less than secretive treatment such as an FCC filing.
GrayShift has found many clients for the GrayKey, as law enforcement grapples with the issue of wanting to gain access to devices owned by suspects, but are unable to secure a passcode or to pass biometrics to do so without the suspect's cooperation. The device has reportedly been used in some high-profile investigations, including one by the FBI in late 2019 where it was allegedly used to gain access to a locked iPhone 11 Pro Max.
In March, GrayShift started to market a software tool that could be used to reveal an iPhone's passcode without cracking the device. The digital forensics tool named "Hide UI" reportedly consists of spyware that can be installed via GrayKey and acts as a keylogger, one that monitors for when the user enters their passcode.

Comments
I value the security of my device but I also know that there are times when the government has a legitimate and legal right to access a device. “Back doors” written into the software (or worse yet, hardware) have been shown to be ineffective. A device like this seems like a reasonable compromise. No, your device is not ‘absolutely’ secure, but it is as secure as one can reasonably expect. My big concern is some reports I saw a while back that the devices are not registered/controlled by the company making them, so there is no guarantee that only legitimate law enforcement agencies are using them.