Swift-based ransomware targets macOS pirates with false decryption promise
New ransomware for the Mac has been discovered by security researchers, with the "poorly coded" malware created in Swift encrypting the user's files and demanding a payment, without any possibility of decrypting the files even if the ransom is paid.
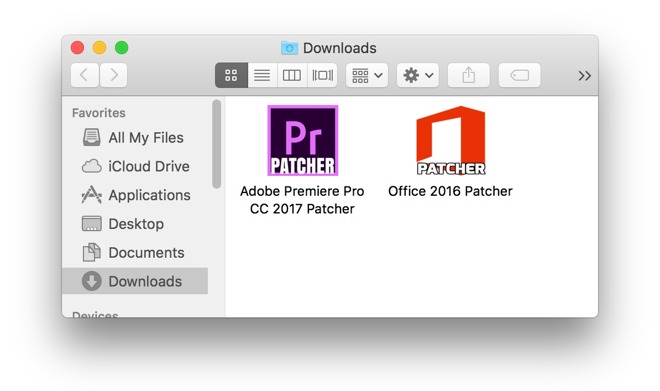
Circulating via BitTorrent sites and called "Patcher," the malware poses as a crack for pirates to get around copy protection and licensing systems used in popular software suites. Researcher Marc-Etienne M.Lveill found two different fake patchers that used the same code, posing as ways to unlock Microsoft Office for Mac 2016 and Adobe Premiere Pro CC 2017, but suggests there may be more instances of the malware circulating around under different names.
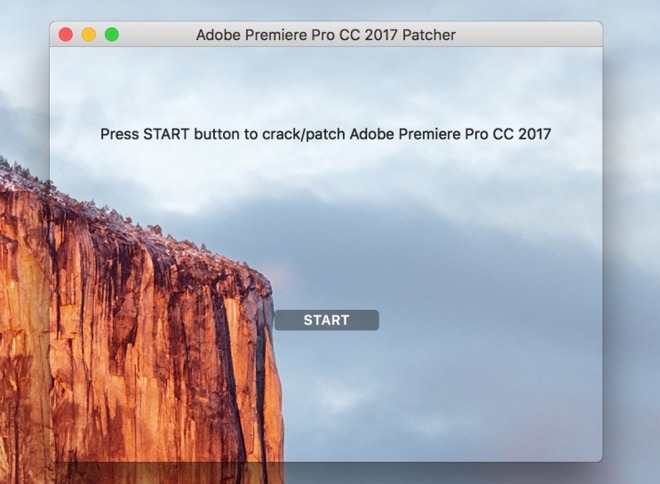
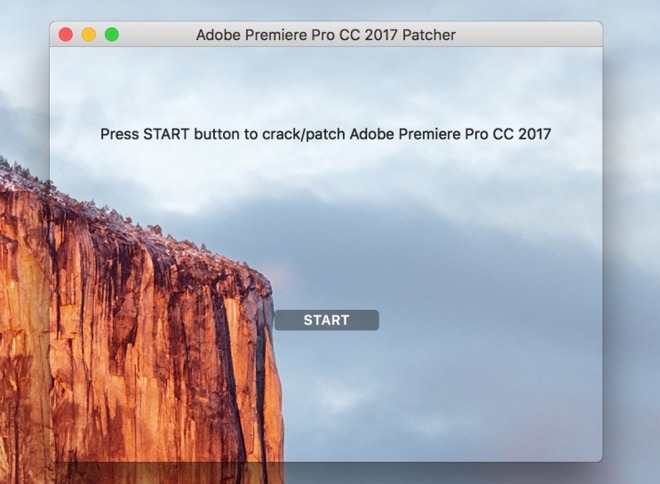
When extracted from the archive and executed, the malware opens up a window advising users to press the start button to patch the pirated software. If clicked, the ransomware then spreads around a "readme" file to various user directories, before encrypting all other user files using a randomly-generated 25-character key in an archive, and deleting the original files.
The Readme file explains to the user the files are encrypted, and to pay 0.25 bitcoin to a specific wallet address to unlock them within seven days. While it is claimed files will be decrypted within 24 hours of the random's payment, another option to pay 0.45 bitcoin is also offered, touting decryption within ten minutes.
The researcher notes the malware is "generally poorly coded" in a number of ways. Produced using Swift, the application's window is impossible to open if it is closed, while code to try and use Disk Utility to null the free space on the root partition uses the wrong path to the tool.
The details within the Readme file are hard coded, meaning all victims are presented with the same bitcoin wallet and email address instead of information unique to each infection. An inspection of the Bitcoin wallet at the time of reporting reveals there have yet to be any transactions, which means no-one has so far paid the creator's ransom.
Unlike many other examples of cryptographic ransomware, it is noted victims will not be able to get their files back by decryption, even if the ransom is paid. There is no code in the malware that sends the key to the operator, so there is no possibility of providing the "service" of decrypting the files for the user, while the length of the key also suggests a brute force attack would take too long to accomplish.
"This new crypto-ransomware, designed specifically for macOS, is surely not a masterpiece," writes Lveill. "Unfortunately, it's still effective enough to prevent victims accessing their own files and could cause serious damage."
Lveill recommends having a current offline backup of all important data, as well as security software, to help protect against similar threats.
"Patcher" is the latest in a string of recently-discovered malware aimed at macOS users. In the last month alone, malware posing as Adobe Flash Player updates and a Microsoft Word macro have been found targeting people in human rights groups and the U.S. defense industry, as well as an Xagent malware package reportedly created by a Russian hacking group.
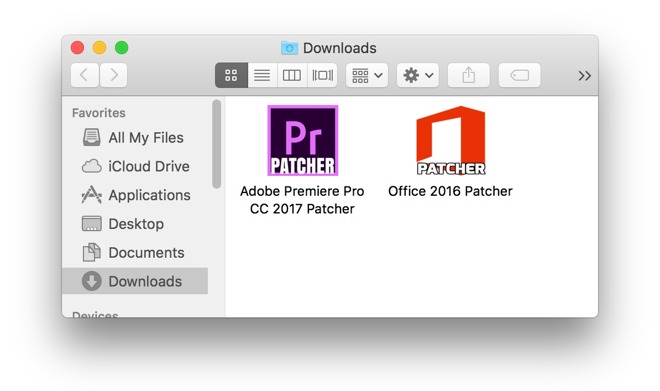
Circulating via BitTorrent sites and called "Patcher," the malware poses as a crack for pirates to get around copy protection and licensing systems used in popular software suites. Researcher Marc-Etienne M.Lveill found two different fake patchers that used the same code, posing as ways to unlock Microsoft Office for Mac 2016 and Adobe Premiere Pro CC 2017, but suggests there may be more instances of the malware circulating around under different names.
When extracted from the archive and executed, the malware opens up a window advising users to press the start button to patch the pirated software. If clicked, the ransomware then spreads around a "readme" file to various user directories, before encrypting all other user files using a randomly-generated 25-character key in an archive, and deleting the original files.
The Readme file explains to the user the files are encrypted, and to pay 0.25 bitcoin to a specific wallet address to unlock them within seven days. While it is claimed files will be decrypted within 24 hours of the random's payment, another option to pay 0.45 bitcoin is also offered, touting decryption within ten minutes.
The researcher notes the malware is "generally poorly coded" in a number of ways. Produced using Swift, the application's window is impossible to open if it is closed, while code to try and use Disk Utility to null the free space on the root partition uses the wrong path to the tool.
The details within the Readme file are hard coded, meaning all victims are presented with the same bitcoin wallet and email address instead of information unique to each infection. An inspection of the Bitcoin wallet at the time of reporting reveals there have yet to be any transactions, which means no-one has so far paid the creator's ransom.
Unlike many other examples of cryptographic ransomware, it is noted victims will not be able to get their files back by decryption, even if the ransom is paid. There is no code in the malware that sends the key to the operator, so there is no possibility of providing the "service" of decrypting the files for the user, while the length of the key also suggests a brute force attack would take too long to accomplish.
"This new crypto-ransomware, designed specifically for macOS, is surely not a masterpiece," writes Lveill. "Unfortunately, it's still effective enough to prevent victims accessing their own files and could cause serious damage."
Lveill recommends having a current offline backup of all important data, as well as security software, to help protect against similar threats.
"Patcher" is the latest in a string of recently-discovered malware aimed at macOS users. In the last month alone, malware posing as Adobe Flash Player updates and a Microsoft Word macro have been found targeting people in human rights groups and the U.S. defense industry, as well as an Xagent malware package reportedly created by a Russian hacking group.

Comments
...guessing they want to be single quotes? I'm on macOS via Safari.
No sympathy from me.
I also get the ? problem on the accented e on Windows 10 using Chrome in the forum only.
Nope. Looks like it's a known issue with the site.
Perhaps the pages need some sort of character set indentifer in their meta tags.
In this particular case I don't have to worry because I don't use cracks, but the next iteration might masquerade as something I *do* use so I'd like to be kept up to date.
The format would be retained by manually copy/pasting the article into a new forum thread. The following is copy/pasted from the article and the accented characters work ok:
"Researcher Marc-Etienne M.Léveillé found two different that used the same code"
It may even be better to copy the HTML source from the article page into the plain text part of the editor using the Toggle HTML View button but the article's images use lazy loading (only loads images after you scroll over them) so it won't copy embedded images over, they'd have to be fixed manually. They can be dragged into place from the article. The main article uses htmlentity encoding for special characters, if you copy Léveillé into the following page and hit the button to encode it, it shows how it's stored in the database:
http://www.freeformatter.com/html-escape.html
There's most likely an automated button to copy it directly to the forum. The function that does that would have to run it through the same forum process that encodes comments first.
It could be deployed anywhere though. Apple needs to start locking down what software can do by default. This doesn't mean locking down the platform, just giving the user more control over it. A program that someone downloads should not be immediately able to encrypt every user-level file on a drive and remove the originals nor should it have network access. The OS should block all software by default and let the user know exactly what it's trying to do and ask for explicit permission. The default should be read and create permissions, no write/erase and no network access, even from trusted developers.
With all the free alternatives (these days) do you really need to pirate MS office?
And why does the story (and headline!) mention Swift? Why should we care what language the developer used to create this malware?
What I like about this malware is that it hurts the credibility of ransomeware in general. If no one trusted ransomware there would be no incentive for bad guys to deploy ransomware.
Don't pirate software. Seems simple enough.
I cannot afford Adobe CC, so I use Pixelmator, which is enough for an amateur like me. I want my Mac to be clean on any pirated software.