Mirai-based DDoS attack highlights benefits of Apple's secure HomeKit platform
A distributed denial of service (DDoS) attack that on Friday severely impacted internet access for many U.S. web denizens was found to be in part enabled by a botnet targeting unprotected "Internet of Things" devices. For Apple, the revelation vindicates a controversial walled garden approach to IoT borne out through the HomeKit protocol.

As detailed yesterday, unknown hackers set their sights on Dyn, an internet management company that provides DNS services to many major web entities.
A series of repeated attacks caused websites including The Verge, Imgur and Reddit, as well as services like HBO Now, and PayPal, to see slowdowns and extended downtimes. Follow-up waves played havoc with The New York Times, CNN, Netflix, Twitter and the PlayStation Network, among many others.
Though Dyn was initially unable to nail down a source, subsequent information published by security research firm Flashpoint revealed the targeted attacks involved a strain of the Mirai malware, reports Brian Krebs. Krebs has firsthand experience with Mirai, as the malware was deployed in a DDoS attack that brought down his website, KrebsOnSecurity, in September.
Mirai searches the web for IoT devices set up with default admin username and password combinations, Krebs says. Once discovered, the malware infiltrates and uses poorly protected hardware to facilitate a DDoS attack on an online entity, in this case Dyn.
Poor security practices are nothing new. Uninitiated or lazy end users have for decades left factory default settings untouched on routers, networked printers and other potential intrusion vectors. But this is different.
"The issue with these particular devices is that a user cannot feasibly change this password," said Zach Wikholm, research developer at Flashpoint. "The password is hardcoded into the firmware, and the tools necessary to disable it are not present. Even worse, the web interface is not aware that these credentials even exist."
To prevent another Mirai attack, or a similar assault harnessing IoT hardware, offending devices might require a recall, Krebs says. Short of a that, unplugging an affected product is an effective stopgap.
By contrast, Apple's HomeKit features built-in end-to-end encryption, protected wireless chip standards, remote access obfuscation and other security measures designed to thwart hacks. Needless to say, it would be relatively difficult to turn a HomeKit MFi device into a DDoS zombie.
Announced in 2014 alongside iOS 8, HomeKit debuted as a secure framework onto which manufacturers of smart home products can lattice accessory communications. Specifically, the system uses iOS and iCloud infrastructure to securely synchronize data between host devices and accessories.
Apple details HomeKit protections in a security document posted to its website (PDF link), noting the system's reliance on public-private key pairs.
First, key pairs are generated on an iOS device and assigned to each HomeKit user. The unique HomeKit identity is stored in Keychain and synchronized to other devices via iCloud Keychain. Compatible accessories generate their own key pair for communicating with linked iOS devices. Importantly, accessories will generate new key pairs when restored to factory settings.
Apple uses the Secure Remote Password (3,072-bit) protocol to establish a connection between an iOS device and a HomeKit accessory via Wi-Fi or Bluetooth. Upon first use, keys are exchanged through a procedure that involves entering an 8-digit code provided by the manufacturer into a host iPhone or iPad. Finally, exchanged data is encrypted while the system verifies the accessory's MFi certification.
When an iPhone communicates with a HomeKit accessory, the two devices authenticate each other using the exchanged keys, Station-to-Station protocol and per-session encryption. Further, Apple painstakingly designed a remote control feature called iCloud Remote that allows users to access their accessories when not at home.
In addition to the above, Apple also integrates privacy safeguards that ensure only verified users have access to accessory settings, as well as privacy measures that protect against transmission of user-identifying or home-identifying data.
At its core, HomeKit is a well-planned and well-executed IoT communications backbone. The accessories only work with properly provisioned devices, are difficult to infiltrate, seamlessly integrate with iPhone and, with iOS 10 and the fourth-generation Apple TV (which acts as a hub), feature rich notifications and controls accessible via Apple's dedicated Home app. And they can't indiscriminately broadcast junk data to the web.
The benefits of HomeKit come at cost to manufacturers, mainly in incorporating Apple's coprocessor, but the price is undoubtedly less dear than recalling an unfixable finished product.

As detailed yesterday, unknown hackers set their sights on Dyn, an internet management company that provides DNS services to many major web entities.
A series of repeated attacks caused websites including The Verge, Imgur and Reddit, as well as services like HBO Now, and PayPal, to see slowdowns and extended downtimes. Follow-up waves played havoc with The New York Times, CNN, Netflix, Twitter and the PlayStation Network, among many others.
Though Dyn was initially unable to nail down a source, subsequent information published by security research firm Flashpoint revealed the targeted attacks involved a strain of the Mirai malware, reports Brian Krebs. Krebs has firsthand experience with Mirai, as the malware was deployed in a DDoS attack that brought down his website, KrebsOnSecurity, in September.
Mirai searches the web for IoT devices set up with default admin username and password combinations, Krebs says. Once discovered, the malware infiltrates and uses poorly protected hardware to facilitate a DDoS attack on an online entity, in this case Dyn.
Poor security practices are nothing new. Uninitiated or lazy end users have for decades left factory default settings untouched on routers, networked printers and other potential intrusion vectors. But this is different.
DVRs and IP cameras like those made by Chinese company XiongMai Technologies contain a grievous security vulnerability and are in large part responsible for hosting the botnet.According to Krebs, DVRs and IP cameras made by Chinese company XiongMai Technologies, as well as other connected gadgets currently flooding the market, contain a grievous security vulnerability and are in large part responsible for hosting the botnet. As he explains, a portion of these devices can be reached via Telnet and SSH even after a user changes the default username and password.
"The issue with these particular devices is that a user cannot feasibly change this password," said Zach Wikholm, research developer at Flashpoint. "The password is hardcoded into the firmware, and the tools necessary to disable it are not present. Even worse, the web interface is not aware that these credentials even exist."
To prevent another Mirai attack, or a similar assault harnessing IoT hardware, offending devices might require a recall, Krebs says. Short of a that, unplugging an affected product is an effective stopgap.
By contrast, Apple's HomeKit features built-in end-to-end encryption, protected wireless chip standards, remote access obfuscation and other security measures designed to thwart hacks. Needless to say, it would be relatively difficult to turn a HomeKit MFi device into a DDoS zombie.
Announced in 2014 alongside iOS 8, HomeKit debuted as a secure framework onto which manufacturers of smart home products can lattice accessory communications. Specifically, the system uses iOS and iCloud infrastructure to securely synchronize data between host devices and accessories.
Apple details HomeKit protections in a security document posted to its website (PDF link), noting the system's reliance on public-private key pairs.
First, key pairs are generated on an iOS device and assigned to each HomeKit user. The unique HomeKit identity is stored in Keychain and synchronized to other devices via iCloud Keychain. Compatible accessories generate their own key pair for communicating with linked iOS devices. Importantly, accessories will generate new key pairs when restored to factory settings.
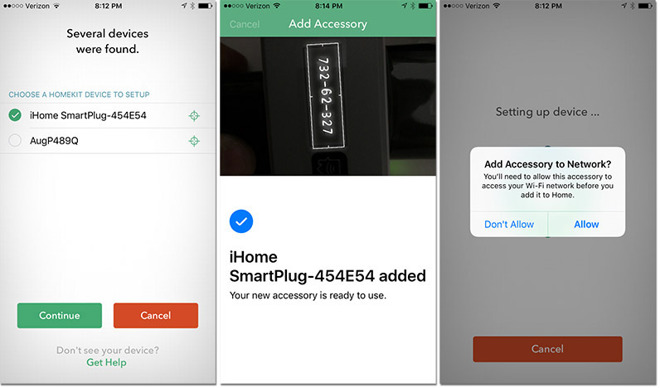
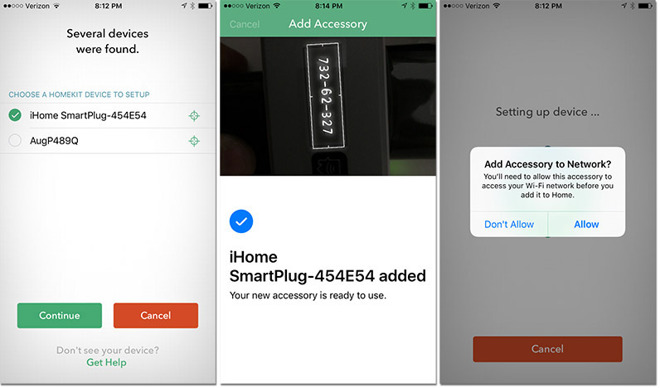
Apple uses the Secure Remote Password (3,072-bit) protocol to establish a connection between an iOS device and a HomeKit accessory via Wi-Fi or Bluetooth. Upon first use, keys are exchanged through a procedure that involves entering an 8-digit code provided by the manufacturer into a host iPhone or iPad. Finally, exchanged data is encrypted while the system verifies the accessory's MFi certification.
When an iPhone communicates with a HomeKit accessory, the two devices authenticate each other using the exchanged keys, Station-to-Station protocol and per-session encryption. Further, Apple painstakingly designed a remote control feature called iCloud Remote that allows users to access their accessories when not at home.
Apple's coprocessor is key to HomeKit's high level of security, though the implementation is thought to have delayed the launch of third-party products by months. The security benefits were arguably worth the wait.Accessories that support iCloud remote access are provisioned during the accessory's setup process. The provisioning process begins with the user signing in to iCloud. Next, the iOS device asks the accessory to sign a challenge using the Apple Authentication Coprocessor that is built into all Built for HomeKit accessories. The accessory also generates prime256v1 elliptic curve keys, and the public key is sent to the iOS device along with the signed challenge and the X.509 certificate of the authentication coprocessor.
In addition to the above, Apple also integrates privacy safeguards that ensure only verified users have access to accessory settings, as well as privacy measures that protect against transmission of user-identifying or home-identifying data.
At its core, HomeKit is a well-planned and well-executed IoT communications backbone. The accessories only work with properly provisioned devices, are difficult to infiltrate, seamlessly integrate with iPhone and, with iOS 10 and the fourth-generation Apple TV (which acts as a hub), feature rich notifications and controls accessible via Apple's dedicated Home app. And they can't indiscriminately broadcast junk data to the web.
The benefits of HomeKit come at cost to manufacturers, mainly in incorporating Apple's coprocessor, but the price is undoubtedly less dear than recalling an unfixable finished product.

Comments
I could see Apple working this into their keynote on Oct 27th and talking up theirs security/privacy. I could also see companies selling HomeKit compatible devices using this in their advertising. This was a real and significant problem that affected a lot of people, and was traced to a very specific cause (cheap home devices with little to no security).
This can only be good for Apple, but they need to promote it better.
This DDOS is only the beginning. There will be more and bigger events before anything is done to improve security.
This is a disaster waiting to happen. To the general public it won't matter if Apple are secure or not, all IOT thingamyjibs will be tarred with the same brush.
There are millions of devices in transit from China. The vast majority will be totally insecure.
I am beginning to wonder if this is the beginning of the end of the internet as we know it.
With millions and millions and millions of devices working together in a DDOS event short of pulling the plug on every home router you can't stop it in a month of sundays.
Some of us have made a stand against all IOT devices Homekit or not. None will be connected to any network I have any control over for the forseeable future.
Most of these systems should be blocked from direct internet access and only permit access via a VPN to the local network.
We are all impacted by this even if our devices are not susceptible to this exploit.
Is there a list on the net of devices that are susceptible?... And no, avoiding all connected devices is not realistic in this day and age.
i don't remember any password prompting on my one....