New iPhone lock screen flaw found in iOS 6.1.3, grants access to address book and photos
Just one day after Apple rolled out the latest iOS 6.1.3, which patched an iPhone lock screen security flaw, a similar bug has been discovered that replicates the bypass albeit in a more involved and limited process.
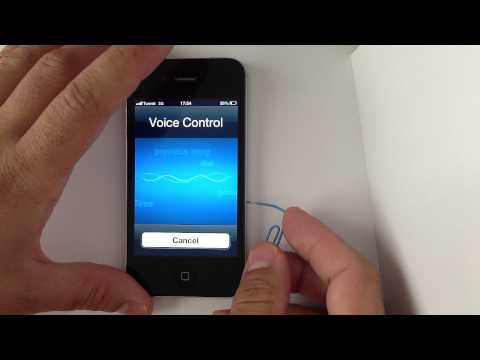
The flaw, found on Wednesday by YouTube user "videosdebarraquito," allows unauthorized users access a locked handset's address book and photos by ejecting the SIM card while using voice control to make a call.
It appears that the flaw is limited to iPhones without Siri support, as AppleInsider was not able to reproduce the behavior on an iPhone 5.
As seen in the demonstration video, the process is somewhat more involved than simply dialing and canceling an emergency call. In order to reproduce the bug, a malicious user must be using an iPhone incompatible with Siri, which has Voice Control activated, and have a paper clip or SIM card extraction tool. By holding down the Home button when an iPhone is locked, a user can request a number to be dialed. When the Voice Control system initiates the call, the removal of the SIM card tray, and thus the SIM card, defaults the phone app back to the dialing screen. From there, contacts, photos and recent call information can be accessed.
When Apple released iOS 6.1.3 on Tuesday, the company patched a similar lock screen bug that bypassed the lock screen security code to give low-level access to contact information and other assets available from the phone app.
While Tuesday's discovery is likely to be fixed in an upcoming iOS update, for now users can simply turn off "Voice Control" in the Settings menu to disallow unwanted iPhone access.
The flaw, found on Wednesday by YouTube user "videosdebarraquito," allows unauthorized users access a locked handset's address book and photos by ejecting the SIM card while using voice control to make a call.
It appears that the flaw is limited to iPhones without Siri support, as AppleInsider was not able to reproduce the behavior on an iPhone 5.
As seen in the demonstration video, the process is somewhat more involved than simply dialing and canceling an emergency call. In order to reproduce the bug, a malicious user must be using an iPhone incompatible with Siri, which has Voice Control activated, and have a paper clip or SIM card extraction tool. By holding down the Home button when an iPhone is locked, a user can request a number to be dialed. When the Voice Control system initiates the call, the removal of the SIM card tray, and thus the SIM card, defaults the phone app back to the dialing screen. From there, contacts, photos and recent call information can be accessed.
When Apple released iOS 6.1.3 on Tuesday, the company patched a similar lock screen bug that bypassed the lock screen security code to give low-level access to contact information and other assets available from the phone app.
While Tuesday's discovery is likely to be fixed in an upcoming iOS update, for now users can simply turn off "Voice Control" in the Settings menu to disallow unwanted iPhone access.


Comments
To be fair, who actually uses Voice Control anyway?
Originally Posted by AppleInsider
…by ejecting the SIM card while using voice control to make a call.
This is probably the stupidest exploit I've ever heard of. This is like Woz getting the students to make weird poses to keep the TV running.
Originally Posted by palegolas
Ousting Scott wasn't such a great idea...
Implying he's somehow leaking all these exploits or that he personally would have been able to prevent them?
I do. Making calls and and for the Music app, mostly.
Quote:
Originally Posted by SolipsismX
Quote:
Originally Posted by hittrj01
To be fair, who actually uses Voice Control anyway?
I do. Making calls and and for the Music app, mostly.
How do you get it to open when Siri is enabled? I tried to ask Siri to open Voice Control and she opened Voice Memos.
Then I asked Siri if I have Voice Control and she replied "I'd rather not say".
I may be using a different definition of Voice Control. Siri has replaced what I consider the old style, localized Voice Control for iOS but I still put in that same category of controlling the device by voice, which I also used extensively for contacts and (the then) iPod app as stated previously.
If that is what you are referring to then I know that Voice Control still exists in devices with Siri but you have to disable Siri which will auto-enable it (and auto-disable it when you activate Siri). I wish the local system was more intelligent so that I didn't have to call the Siri servers for items like contacts and playing a album, artist or playlist. Even on LTE with the iPhone 5 it seems noticeably slower than Voice Control on the iPhone 4 for that same task.
Quote:
Originally Posted by palegolas
Ousting Scott wasn't such a great idea...
Quote:
Originally Posted by Tallest Skil
Implying he's somehow leaking all these exploits or that he personally would have been able to prevent them?
Some people just can't stop themselves from spewing nonsense. The Internet does this to people.
Quote:
Originally Posted by mstone
How do you get it to open when Siri is enabled? I tried to ask Siri to open Voice Control and she opened Voice Memos.
Then I asked Siri if I have Voice Control and she replied "I'd rather not say".
Well, the article does say that the exploit does not work on phones with Siri support. AI couldn't get it to work on an iPhone 5.
Quote:
Originally Posted by lkrupp
Well, the article does say that the exploit does not work on phones with Siri support. AI couldn't get it to work on an iPhone 5.
I be willing to bet it will break on an iPhone 5 too if you disable Siri. I'm not going to try it.
Quote:
Originally Posted by Yojimbo007
How do they figure these things out? Mind boggling!
They must have A LOT of extra time on their hands doing huge numbers of trial and error until they get something.
Hours upon hours of time wasted....just for their 15 minutes?
This sh*ts getting to be a joke.
Considering AI didn't state that they disabled Siri so that the old Voice Control could take over makes it highly likely they didn't.
I'm also not going to test it.
I wasn't going to say anything but the bigger story is that Voice Control understood what he was saying.
The average user is still likely to disclose more personal information to a broader audience by installing a single android application.
I agree with others here.. This smells like shill bait by Same-sung... Funny all these exploits seem to coincide with Same-sungs "SAFE" multi million dollar marketing push???
Quote:
Originally Posted by mstone
How do you get it to open when Siri is enabled? I tried to ask Siri to open Voice Control and she opened Voice Memos.
Then I asked Siri if I have Voice Control and she replied "I'd rather not say".
Voice control (and thus this bug) is only used on old model phones now. If you use Siri or have an iPhone 5 this exploit doesn't work.
So the group affected is users with old hardware or who haven't updated the OS in a long time who also have voice control enabled and also happen to lose their phone and the guy that finds the phone is a criminal and he knows about this exploit because he's a geek and has a SIM ejection pin handy in his pocket. Even then, he will only be able to see your address book and your camera roll.
So … yeah, really gigantic security hole. /s