Macs 'partially affected' by unpatchable Thunderbolt security exploit
A security researcher has discovered a Thunderbolt vulnerability that could allow attackers to bypass system defenses and access the contents of a locked computer's drive in minutes -- with Boot Camp installs of Windows and Linux susceptible to the attack.
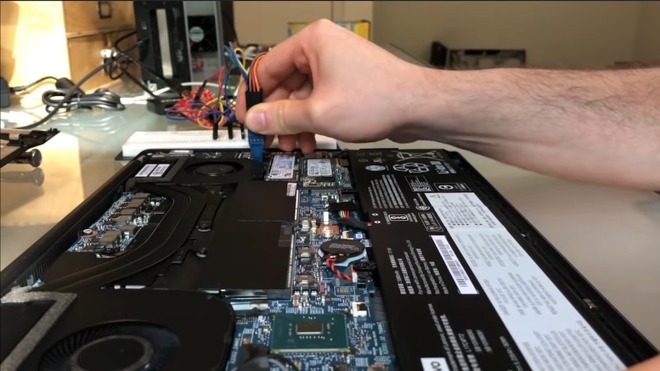
With just a few minutes of physical access to a laptop, Thunderspy could allow an attacker to bypass all of its security and encryption mechanisms. Credit: Bjorn Ruytenberg
Developed and maintained by Intel, Thunderbolt is a common port standard found in millions of consumer PCs, including Apple Macs. Certain features of the Thunderbolt interface have raised concerns among security experts for years, however.
On Sunday, Bjorn Ruytenberg, a security researcher at Eindhoven University of Technology, published details about a new vulnerability he's dubbing "Thunderspy." With just a few minutes of physical access and a couple of hundred dollars of easily purchased equipment, the vulnerability could allow an attacker to bypass a computer's security mechanisms -- even if it's locked and its hard drive is encrypted.
Ruytenberg demonstrated a proof-of-concept of the Thunderspy flaw, which allows attackers to disable the Security Levels feature of Thunderbolt standard, on a Lenovo Thinkpad in a YouTube video.
The process involves unscrewing the backplate of the laptop, interfacing with the Thunderbolt controller with a single-board computer, rewriting the controller firmware and disabling security features. As a result of the exploit, Ruytenberg was able to bypass the password lock screen on the device in just five minutes.
It's a good example of what security experts call an "evil maid attack," which refers to types of hacking that require physical access to a device -- such as a laptop left alone in a hotel room.
The vulnerability, which is unpatchable by software, affects all Thunderbolt-equipped PCs manufactured before 2019, though macOS devices are only "partially affected." That's because Apple's macOS uses its own security mechanisms, such as a device whitelist, IOMMU virtualization and Kernel Direct Access Memory (DMA) protections.
Vulnerabilities in Intel's Thunderbolt connector standard aren't new, and researchers have long been concerned about speed-enhancing features like more direct access to a system's memory. In early 2019, researchers published a flaw dubbed "Thunderclap" that could allow USB-C or DisplayPort devices to compromise Mac and other PC systems.
In the wake of that vulnerability, researchers recommended that users take advantage of an Intel security feature called "Security Levels" -- the exact mechanism that Thunderspy allows attackers to bypass.
Intel claims that it addressed the vulnerability last year, but Wired found that its security fix hasn't yet been widely implemented in many machines.
Ruytenberg has also created a tool called Spycheck for Windows and Linux, which allows consumers to test whether their machines are vulnerable. If they are, he recommends disabling Thunderbolt ports entirely as the only real way to mitigate the flaw.
The Thunderbolt 3 protocol is also due to be added to USB4, which means that upcoming computers and accessories could be impacted by Thunderspy. Ruytenberg notes that more testing is required to confirm that, however.
The Thunderbolt flaw still leaves macOS devices vulnerable to some security workarounds, such as cloning the identity of a device on Apple's peripheral whitelist to an attacker device. That could open the door to other types of exploits similar to BadUSB, which describes a series of port-based attacks delivered by malicious USB devices.
Exploiting the vulnerability on macOS is still going to require physical access to a device, and since the scope of the attack is more limited on Apple's software due to built-in protections, the average macOS user is at a lower risk than those that run Windows or Linux. It's really only going to be a concern for already high-risk individuals.
While most macOS users are going to largely safe from most of the repercussions of the vulnerability, it's still a good idea to avoid plugging in untrusted peripherals or storage devices, and control of physical access to devices remains paramount.
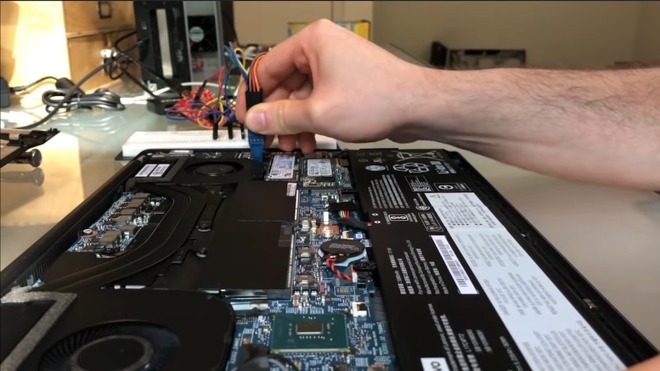
With just a few minutes of physical access to a laptop, Thunderspy could allow an attacker to bypass all of its security and encryption mechanisms. Credit: Bjorn Ruytenberg
Developed and maintained by Intel, Thunderbolt is a common port standard found in millions of consumer PCs, including Apple Macs. Certain features of the Thunderbolt interface have raised concerns among security experts for years, however.
On Sunday, Bjorn Ruytenberg, a security researcher at Eindhoven University of Technology, published details about a new vulnerability he's dubbing "Thunderspy." With just a few minutes of physical access and a couple of hundred dollars of easily purchased equipment, the vulnerability could allow an attacker to bypass a computer's security mechanisms -- even if it's locked and its hard drive is encrypted.
Ruytenberg demonstrated a proof-of-concept of the Thunderspy flaw, which allows attackers to disable the Security Levels feature of Thunderbolt standard, on a Lenovo Thinkpad in a YouTube video.
The process involves unscrewing the backplate of the laptop, interfacing with the Thunderbolt controller with a single-board computer, rewriting the controller firmware and disabling security features. As a result of the exploit, Ruytenberg was able to bypass the password lock screen on the device in just five minutes.
It's a good example of what security experts call an "evil maid attack," which refers to types of hacking that require physical access to a device -- such as a laptop left alone in a hotel room.
The vulnerability, which is unpatchable by software, affects all Thunderbolt-equipped PCs manufactured before 2019, though macOS devices are only "partially affected." That's because Apple's macOS uses its own security mechanisms, such as a device whitelist, IOMMU virtualization and Kernel Direct Access Memory (DMA) protections.
Vulnerabilities in Intel's Thunderbolt connector standard aren't new, and researchers have long been concerned about speed-enhancing features like more direct access to a system's memory. In early 2019, researchers published a flaw dubbed "Thunderclap" that could allow USB-C or DisplayPort devices to compromise Mac and other PC systems.
In the wake of that vulnerability, researchers recommended that users take advantage of an Intel security feature called "Security Levels" -- the exact mechanism that Thunderspy allows attackers to bypass.
Intel claims that it addressed the vulnerability last year, but Wired found that its security fix hasn't yet been widely implemented in many machines.
Ruytenberg has also created a tool called Spycheck for Windows and Linux, which allows consumers to test whether their machines are vulnerable. If they are, he recommends disabling Thunderbolt ports entirely as the only real way to mitigate the flaw.
The Thunderbolt 3 protocol is also due to be added to USB4, which means that upcoming computers and accessories could be impacted by Thunderspy. Ruytenberg notes that more testing is required to confirm that, however.
What Thunderspy means for Mac users
In practical terms, attackers won't be able to disable the macOS lock screen or perform other attacks like they could if they had physical access to the device, as long as a user is running macOS instead of Windows or Linux via Boot Camp. Macs running Windows or Linux on Boot Camp, however, are just as vulnerable as other PCs.The Thunderbolt flaw still leaves macOS devices vulnerable to some security workarounds, such as cloning the identity of a device on Apple's peripheral whitelist to an attacker device. That could open the door to other types of exploits similar to BadUSB, which describes a series of port-based attacks delivered by malicious USB devices.
Exploiting the vulnerability on macOS is still going to require physical access to a device, and since the scope of the attack is more limited on Apple's software due to built-in protections, the average macOS user is at a lower risk than those that run Windows or Linux. It's really only going to be a concern for already high-risk individuals.
While most macOS users are going to largely safe from most of the repercussions of the vulnerability, it's still a good idea to avoid plugging in untrusted peripherals or storage devices, and control of physical access to devices remains paramount.


Comments
As the article mentioned, it's because Windows and Linux machines make use of the security features that are built into the Thunderbolt controller firmware. macOS does not - it uses Apple's own security system.
"...The system becomes vulnerable to attacks similar to BadUSB. Therefore, MacOS is partially affected."
EDIT: Well this is somewhat surprising, Microsoft is well aware that Thunderbolt security is lacking which is why Surface computers won't offer it. A few weeks ago they were asked "why not" and an MS engineer answered.
"No Surface device has Thunderbolt. Why not? Because that’s a direct memory access port,” explains the Microsoft employee. “If you have a well prepared stick that you can put into the direct memory access port, then you can access the full device in memory and all data that’s stored in memory. We don’t believe, at this moment, that Thunderbolt can deliver the security that’s really needed from the devices.”
That said, there are "no user serviceable parts within", so generally not much point in opening up a current laptop.
A Mac is a Intel based computer capable of running OSX, Windows or Linux. What makes it a Mac is some very specific hardware that OSX is ideally suited to take advantage of.