nicholfd
About
- Username
- nicholfd
- Joined
- Visits
- 81
- Last Active
- Roles
- member
- Points
- 1,658
- Badges
- 0
- Posts
- 832
Reactions
-
Review: macOS Catalina 10.15 is what Apple promised the Mac could be, and is a crucial upg...
You are not approving access to your Downloads folder. You are giving that specific website permissions to download files (to wherever you have designated as the default download location). This stops drive-by downing of malware, etc., where as soon as you click a link or open a web page, software is downloaded, and if it's considered "safe", it is automatically opened.Metriacanthosaurus said:
After 15 years of downloading things in Safari, you now get the "feature" of having to approve access to your Downloads folder, manually, for every single website.








-
New 2021 12.9-inch iPad Pro can't use previous Magic Keyboard
I think your info is for the "new", updated version. It is compatible with the three generations. Just above the "Magic Keyboard", see the red "New" indicator?GuruZac said:This article is bogus. See Apple's product info and compatibility on their own website...
https://www.apple.com/ipad-keyboards/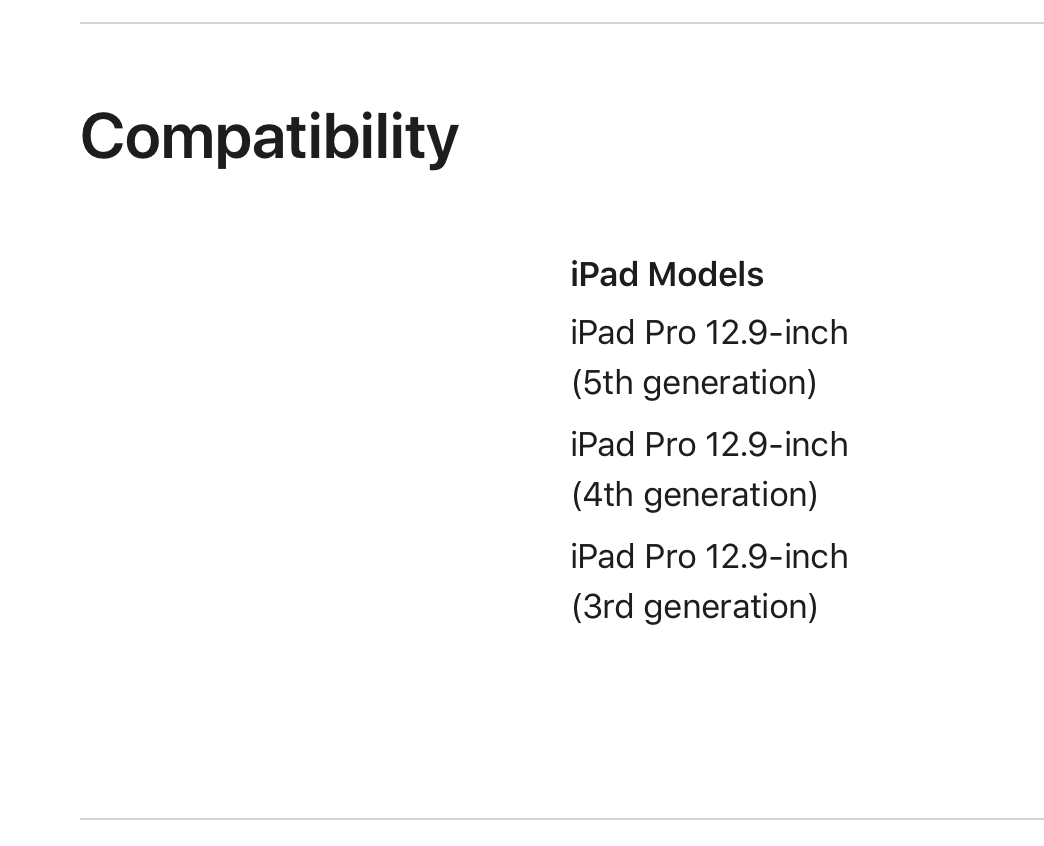





-
Apple capitulates to Russia laws requiring preinstalled software on iPhone, Mac
The title, "Apple agrees to Russia laws requiring preinstalled software" doesn't match the content:
"Under the agreement, iPhones and iPads activated from April 1 onward will present a new screen to users, offering a selection of applications produced by Russian developers. Users will be able to select which apps they will allow or refuse to be installed via this screen as part of the set-up process."
There is nothing preinstalled, if the body/content is correct. Just an offer to install apps, which the user can refuse.









-
Microsoft pits Surface Pro 7 against MacBook Pro in new ad
WTF are you talking about? I write code on an iPad all the time (Python, Perl, PHP, BASH, etc.) - there are many fine code editors (VSCode is not one of them & Atom is ok) and there is even a Python IDE that actually runs Python code - Pythonista 3 & a version for Python 2. Here is a PHP IDE I've used on an iPad - DraftCode Offline PHP IDE.cloudguy said:You can't even do something simple like install VSCode or Atom and write Javascript or Python code on an iPad.
VSCode on macOS is a PoS - doesn't even follow standard keyboard shortcuts. It's just a poorly ported Windows app.
I tried Atom on macOS for some embedded development - another poorly ported app, with some good ideas, but if things like undo/redo don't follow standard Mac app conventions - WTF?!?!?




-
Apple advises iPhone 5 owners to update to iOS 10.3.4 by November 3
This is an up date to keep time accurate. GPS is used for time. Security (signing, certificates, etc.) all require accurate time, or things like the App Store, iCloud, etc., do not work. This update fixes a GPS time issue because GPS' have "rollovers" where some hardware/software may have bugs, or did not considered the devices being in use this long. Without this update, the device date/time will be wrong and secure stuff will break (App Store, iCloud, iMessage, secure e-mail, etc.)GeorgeBMac said:
Well, they aren't -- but, in this case, Android and Apple work about the same. Google updates its systems but, at least partly because so many phones are using customized versions of the code many of those phones have to be updated by the carrier -- which doesn't happen. Actually the best of the two is neither -- it is Microsoft: I'm typing this on a 10 year old machine running the latest version of Windows -- and I have even older machines running current versions as well.wood1208 said:
Because Apple is not Android OS or Android phone maker.GeorgeBMac said:I'm a little confused by this. I thought Apple had halted updates to the iPhone 5 last September (2018). Is it still getting updates? Or maybe just security updates?
But, none of that answered my original question of: "What is Apple's policy regarding outdated equipment? I thought they had halted updates to the iPhone 5."



-
New AirPods firmware enables Spatial Audio, automatic switching
Um... No. Your router has nothing to do with AirPods - they can't see or use your router. The AirPods are bluetooth only and work through your iPhone/iPad/Mac to receive the update. Proximity to your router has absolutely zero to do with getting the AirPods updated.iOS_Guy80 said:
I think he means just have the AirPods paired to a device. The closer they are to your router the sooner the update will occur.caladanian said:“ So long as the AirPods Pro are in the charging case and connected to an iOS device” - how can they be in the case and at the same time connected?





-
Qualcomm says its Apple Silicon rival chips will be in PCs by late 2023
Nope - they announced they are 3-years behind Apple.designr said:Lemme see if I have this right.
Qualcomm just announced that they are 2-years behind Apple.
Did I get it right?
They stated late, 2023 for consumer product release. M1 mini & MacBook Air were released late 2020 (got mine November, 2020).



-
M1 benchmarks prove Apple Silicon outclasses nearly all current Intel Mac chips
That 8th GPU core is probably not "disabled". One of the 8 x cores is probably defective, and this is Apple's way of using the whole system on a chip, instead of scrapping it. This is common in both CPU & GPU manufacturing.randominternetperson said:
What are you basing that on? Based on the numbers DuhSesame (re)posted, the pro and the mini are identical--even with the 30-minute test. Calling 7763 versus 7716 a "slight advantage" is like saying that something selling for $99.39 is "slightly cheaper" than something selling for $100.00. While technically true, a 0.6% difference just statistical noise.dewme said:The MacBook Pro's slight advantage over the Mac Mini tells me that Apple could probably tweak a lot more performance from the Mini if they were willing to sacrifice a bit on its aesthetics to have a more aggressive thermal management subsystem. Maybe a mini cheese grater design rather than the current cigar box design?
What these results tell me is that the M1 chip inside all the new Macs are identical (except in terms of memory and that sadly disabled 8th GPU core in the entry-level air), and that (unlike the very first MacBook Air, way back when) the lack of a fan not a huge deal (9% difference at 10 minutes, 18% different at 30 minutes).



-
Apple issues updates to Pages, Numbers, Keynote
The discussion was about mail merge. Mail does not mean paper. Not seeing it yet, I assume the "new" mail merge functionality of Pages includes the ability to use it for e-mail, not just printed, paper mail.fastasleep said:
Why would you be mailing personalized documents generated in Pages via email? Can Pages send emails? I'm confused.nicholfd said:
You must not realize that mail merge is also used for e-mail, not just paper mail...spheric said:Mail merge!?
It took them A DECADE to reinstate this?
It used to be that you could just drag a contact group directly from Address Book and drop it into an address field in any Pages or Numbers document, and - presto! - it would auto-generate a mailing to all of those recipients, including the proper salutation.
No, I'm not imagining this — they removed the feature (along with super easy trackpad-based resize and rotate) back when they feature-synced iOS and Mac versions of iWork.
So cool that they finally re-implement this essential functionality, years after it has almost entirely ceased to be useful, as paper mailing lists have long died for anything except weddings and funerals…
I haven't used it for paper mail in ages. I do use it periodically for e-mail.
In a business settings, I have various (random, depending on the purpose) groups of employees that need information, or I need information from. I do an export/extract of the employees e-mail address, first name, last name, etc. I can then use mail merge to send "personalized" e-mails to all the individual employees.
Note I didn't mention Pages in my original reply. My reply was about the usefulness of mail merge & use with e-mail. I use this periodically with Word, in the Windows environment. I would also find this useful on my personal Macs, for family, groups, etc. I assume the Pages "new" merge feature will also support e-mail, with mail merge.



-
Qualcomm says its Apple Silicon rival chips will be in PCs by late 2023
You must not realize they do not do that now. You have one O365 subscription, and it's cross platform/architecture.waveparticle said:
Microsoft will gladly support. Because it can charge PC users again for the ported Office suite.blastdoor said:This the most interesting potential development in the PC CPU space since Ryzen (potentially more interesting, really).
Qualcomm doesn't have to beat Apple to succeed, they just have to beat Intel. Major factors affecting this outcome include:
1. Do they get strong support from Microsoft?
2. Does TSMC retain the process lead over Intel?
3. Do developers port and optimize?
My guesses:
1. Sort of...
2. Yes.... barely
3. Some key developers do... most second tier don't
And so the result will be:
moderate success, enough to keep trying.
On whatever platform (OS)/architecture, you just log in with your Microsoft O365 credentials, in the Office apps.